There are two basic parts of managing information:
Making sure it’s stored correctly and that it’s accessible
and
Controlling who can access and change it
The education space typically pays a lot of attention to the first part and not enough attention to the second. Everybody knows about 7×24 and backups, but most institutions evaluate their enterprise systems to make sure they’re covered. However, managing access to information is often not handled by an enterprise-wide approach.
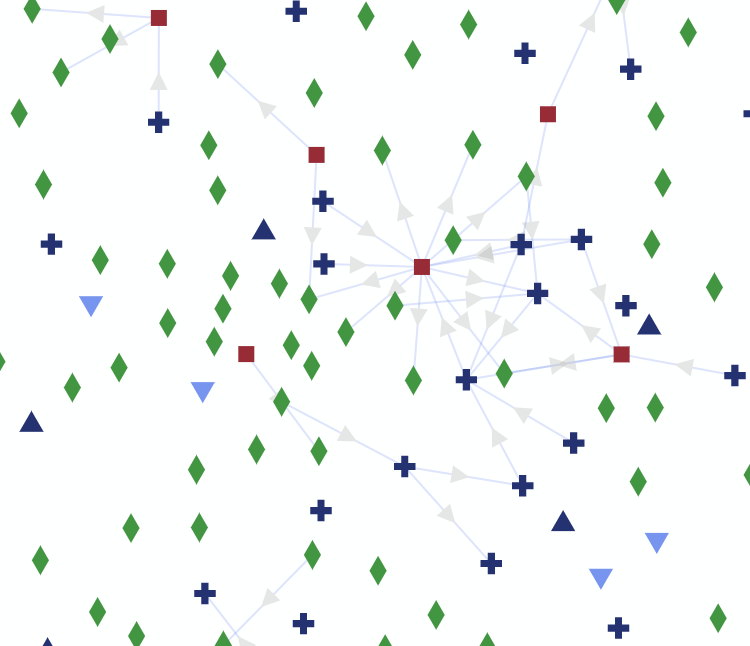
Controlling access is often left to technical people in each functional area to take manage and maintain. Answering questions like “who has access to HR information?” and “what does Bob have access to?” are often difficult to answer. How it gets answered usually varies from system to system.
Granting access to information, especially sensitive information, is a critical business process. It should be clear what the process is, and who holds what responsibility. The decisions should be recorded, so they can be reviewed.
Although this can seem like an impossible goal, since every system is different, its best to break it apart in order to make progress. The first thing is to separate out enforcing the rule from recording the rule.
What is the best way to record the access control business decision? Step one is to record who is allowed to do what in what context. Additionally, who decided it and when, and over what time it is effective. Forcing a clear, structured recording of the business decision can be done across a variety of systems. Of course, the rule needs to be written in a way that it can technically be implemented and enforced.
The first stage might be manual – formalizing the recording of the structured authorization rule – and then using that rule to guide the set up of the system access control. The technical control can be compared to the business rule periodically to ensure they align.
Eventually, this process can be automated so that the authorization rule system is integrated and actually drives the local system access control. The goal of an enterprise authorization system, especially one that manages the authorizations everywhere, maybe a long way away, but it should not be an excuse to not start managing parts of the process correctly in the present.
Your institution can start by defining the process and the rules around your most critical information. Doing this first will go a long way towards getting a handle on managing access. Try to make the rules and process as straight forward and simple as possible so that they may be adopted and understood by the organization at large. Bringing clarity to the process is a benefit itself. It is also a prerequisite for automating the enforcement of the rules. Its time to make this part of managing information consistent across the organization.